Technical Resources
Educational Resources
APM Integrated Experience
Connect with Us
By adopting a cloud syslog solution, tech pros can leverage the popular syslog standard to centralize—and use—log data on a flexible remote platform.
Tech pros who have to deal with log data need a centralized management solution. They need to bring together reams of log data, which typically means using the syslog standard. Syslog has long been a useful, flexible, and reliable way to send event messages, and users need a log management solution they can configure to integrate with this common standard.
In many cases, collecting and centralizing a large volume of event messages on a local syslog server can be a suboptimal solution. With so many aspects of IT infrastructure generating log data, an organization’s storage needs alone can quickly become both costly and unmanageable. Since they offer robust features and more flexibility than local syslog servers, cloud syslog solutions are many tech pros’ preferred choice for log management and monitoring.
Syslog is a widely used standard for sending event messages (typically to a central syslog server where the messages can be collected, stored, and used). Syslog was developed by Eric Allman in the 1980s and has since become the built-in standard for log management on Unix and Linux. While syslog is not native on Windows, tech pros often use third-party tools to collect and forward Windows event log data over syslog.
Syslog event messages can include information like IP address, timestamp, event content, and severity level. This syslog data can come from sources like routers, firewalls, workstations, web applications, and operating systems. As a standard, syslog allows for a distinction between the elements generating the messages, the system storing the messages collected from various sources, and the tools performing analysis. It uses a client-server architecture, sending messages from the designated clients to the defined server location whenever events are triggered.
A cloud syslog solution is often a more robust and flexible way to manage and monitor syslog files. Dealing manually with decentralized (distributed) event logs can be an overly time-consuming process. To deal with even a moderate volume of logs, you need to centralize the logs while streamlining and standardizing their management. This means gathering syslog messages from across your IT infrastructure, then centrally storing, viewing, and using this information effectively.
To gather syslog event message data, syslog messages can be sent to syslog servers either inside or outside your network. When you keep syslogs at the local level, you may use up disk space quickly, or be forced to limit the amount of detail you record in system logs. You’ll also have to continually make sure to delete log archives. To avoid this management hassle, it’s typically worth it to forward local log messages to a remote syslog server capable of handling all the data. This external syslog server can then store the logs and allow tech pros to use them for troubleshooting and monitoring.
A syslog cloud solution provides the storage, security, and flexibility technicians need. With a cloud platform, there’s no need to invest in extra storage hardware, and as a business grows, the cloud platform scales automatically. Additionally, web consoles make it easy to access your syslog monitoring tools from anywhere—and simple to set up proxies to forward logs for sources without access to the internet.
In short, a cloud log management platform functions as a syslog server, but provides additional log centralization, storage, management, and monitoring features. To facilitate effective management, a remote syslog tool should offer configurable options and functions—customized filtering and alerting go a long way when managing a large volume of system logs.
Typically, a cloud log management platform can integrate with logs sent in either a syslog form or HTTP. When using SolarWinds® Loggly®, tech pros can send any sort of text-based log data to the platform—including both unstructured and structured logs. When configuring your system to send logs, there are a couple different ways to send messages over syslog. Loggly supports both of the following:
– UDP: Previously, the User Datagram Protocol (UDP) was the most common transport layer protocol. With UDP, the server listened to protocol requests from clients on port 514. This was appropriate for sending even large volumes of data within a network with minimal data loss. However, UDP lacked mechanisms for controlling message traffic, and it wasn’t unusual for some logs to get lost. Even when supported, UDP is rarely preferable for external syslog programs.
– TCP/TCP with TLS: It has become more common to use the Transmission Control Protocol (TCP)—most commonly with Transport Layer Security (TLS) encryption—which works over port 6514. TCP helps ensure message delivery, and is considered more reliable for use between networks, as it retransmits data in cases of failure. The added protection of TLS makes TCP a good choice for ensuring your logs aren’t compromised while in transit.
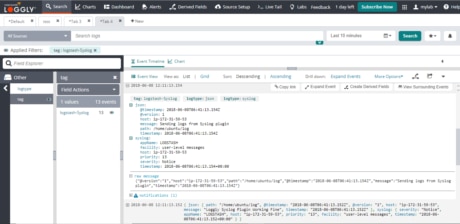
SolarWinds Loggly is a cloud-based syslog server monitoring tool that serves as a user-friendly and feature-rich solution to typical log management problems. This robust tool provides the benefits of cloud log storage while offering the customizable tools tech pros need to perform effective log administration across their networks.
This cloud syslog solution provides tech pros with options for how they configure log inputs. Syslog is the most common way to send logs into Loggly, and depending on your requirements, there are a few ways to use the standard. For instance, you can use a local syslog logger to centralize, collect, and forward log data to Loggly. This is a useful option if you anticipate having trouble connecting your infrastructure to outside endpoints. It’s easy to download a third-party agent on Windows, and Linux systems come with a pre-installed agent. With just a few lines of code, your applications will write to this agent, which will then send or stream logs to Loggly. (In some cases, applications or devices like routers and firewalls may not be able to send data to the syslog agent, but you can configure the agent to “watch” such log files and forward changes to Loggly.)
Additionally, if the applications support the functionality, you can stream logs over syslog without agents, and tech pros can configure custom applications to logger remote syslog by leveraging syslog libraries. You can also set up a local in-memory queue for undelivered messages. Loggly syslog endpoints accept either UDP or TCP syslog. The syslog events must have a RFC5424-compliant header and include your customer token. Further, you can use syslog, syslog-ng, or rsyslog depending on your requirements—both syslog-ng and rsyslog offer additional content filtering capabilities and TCP encryption.
If you’re looking for a cloud syslog program, Loggly offers the features you need. You can set up syslog event logging based on your system requirements with the program’s range of configuration options. Then, you can quickly start monitoring logs throughout your network and managing large numbers of logs with time-saving batch options. Since SolarWinds Loggly is a cloud platform, you needn’t worry about scaling storage—you’ll enjoy all the benefits of a robust, well-managed cloud solution, even as your network grows.
On the hunt for more? Don’t forget to visit the SolarWinds Kiwi Syslog Server